TL;DR
IT Asset Disposition (ITAD) is the process of securely retiring end-of-life technology — covering data destruction, refurbishment, and responsible recycling. With the average data breach now costing $4.44 million according to IBM’s 2025 Cost of a Data Breach Report, proper ITAD isn’t optional — it’s a financial and legal imperative. Choose a certified ITAD provider with documented chain-of-custody, NAID AAA certification, and a commitment to reuse over recycling to protect your data, your budget, and the environment.
Table of Contents
- What Does the ITAD Process Look Like?
- Why Should Your Organization Use an ITAD Provider?
- What Should You Look for in an ITAD Provider?
- What Are the Best ITAD Practices for Organizations?
- FAQ
- Get Your ITAD Questions Answered Today
Introduction
A single retired laptop sitting in a storage closet doesn’t look dangerous. But multiply that by thousands of devices across your organization — each containing sensitive data, hazardous materials, and recoverable value — and you’re staring at a liability that can cost millions.
According to IBM’s 2025 Cost of a Data Breach Report, the average data breach costs organizations $4.44 million. Meanwhile, the world generates 62 million tonnes of e-waste every year, according to the UN Environment Programme — a figure expected to reach 82 million metric tons by 2030. That’s an enormous volume of toxic materials heading for landfills and an enormous volume of sensitive data heading for… who knows where.
IT Asset Disposition (ITAD) exists to solve both problems simultaneously. It’s the structured process of securely and responsibly retiring outdated IT equipment — protecting your organization from data breaches and regulatory fines while keeping hazardous e-waste out of the environment. Proper ITAD has evolved from a recommended practice to an essential component of modern business operations. This guide walks you through the full lifecycle, from what ITAD looks like in practice to how to choose the right provider and build a strategy that protects your data, your bottom line, and the planet.
What Does the ITAD Process Look Like?
Professional ITAD follows a structured lifecycle that transforms the complex task of retiring technology into a manageable, secure, and value-generating process. Here’s how it works, stage by stage.
Inventory and Asset Collection
The process begins with comprehensive inventory management. ITAD providers assess and collect all retiring assets — from individual laptops to entire server systems. Upon arrival at their facility, each asset’s specifications are meticulously documented: make, model, and serial number. This detailed cataloging establishes a clear chain of custody and enables precise tracking throughout the disposition process.
Secure Data Sanitization
Data security stands as the most critical phase of ITAD. Providers employ multiple layers of verified data sanitization methods that adhere to NIST 800-88 guidelines. These include secure data wiping that overwrites information multiple times, degaussing that magnetically erases data from storage devices, and physical destruction methods like shredding or crushing for devices requiring complete elimination.
Each method undergoes external verification by independent experts to ensure effectiveness and maintain compliance with global security standards.
Testing and Refurbishment
Following data sanitization, providers conduct thorough testing to determine each asset’s potential for reuse. This evaluation considers device condition, market demand, and potential return on investment. Assets that pass testing move to refurbishment, where they’re restored to working condition.
This refurbishment process extends device lifespans and creates opportunities for value recovery through remarketing — supporting both environmental sustainability and financial goals. It’s the difference between a throwaway culture and a circular economy.
End-of-Life Recycling
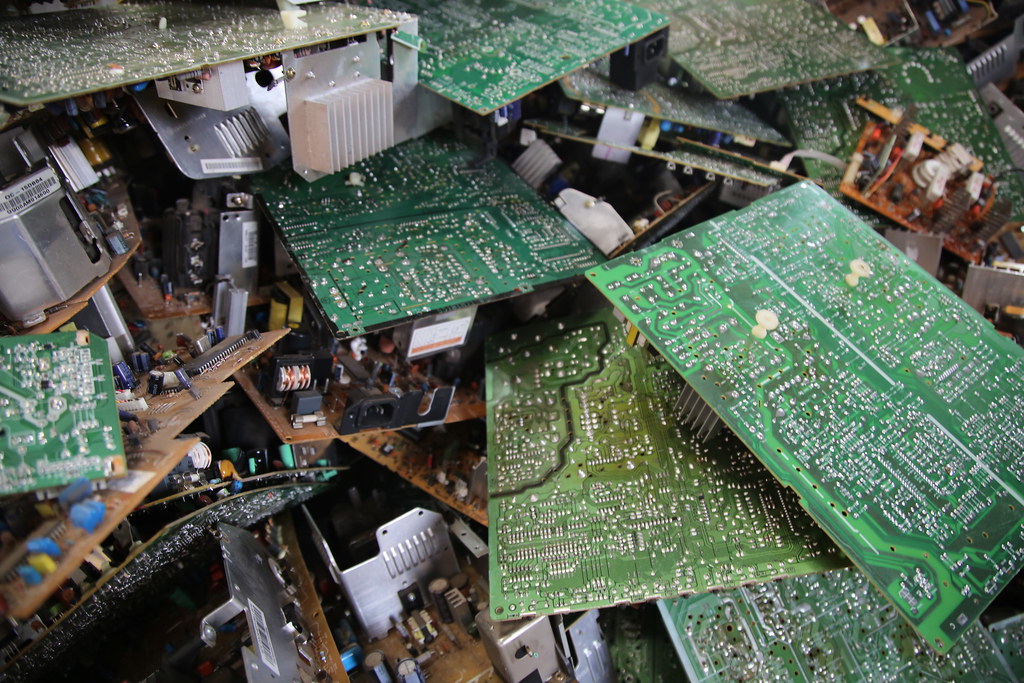
For equipment that cannot be refurbished, responsible recycling becomes the final destination. ITAD providers carefully dismantle these assets to recover valuable materials while safely containing hazardous components like lead, mercury, and cadmium. This methodical processing prevents environmental contamination and ensures compliance with environmental regulations while maximizing material recovery.
Throughout each stage, professional ITAD providers maintain detailed documentation and reporting. This transparency enables organizations to demonstrate compliance with data protection and environmental regulations while tracking the complete lifecycle of their retired assets.
Why Should Your Organization Use an ITAD Provider?
Because the cost of not using one — in dollars, legal liability, and environmental damage — dwarfs the investment. Here’s the breakdown.
Data Security and Compliance
Cybercriminals are always looking for ways to strike it rich. And for them, information is gold. Effective ITAD practices help avoid fines and penalties associated with non-compliance with data protection and environmental regulations. Companies that fail to adhere face costly repercussions, including legal liabilities and reputational damage.
And when we say costly, we mean it. According to IBM’s 2025 Cost of a Data Breach Report, the average data breach sets companies back a staggering $4.44 million. That’s a potential business-ending disaster for many organizations.
ITAD ensures your company stays compliant with regulations like GDPR, HIPAA, and SERA. It also provides clear evidence of your compliance efforts — invaluable in the event of an audit or legal challenge.
Cost Savings and Revenue Recovery
A strategic ITAD program transforms technology disposal from a cost center into a value-generating operation. By outsourcing to specialized vendors, organizations eliminate internal costs for staff training, equipment maintenance, and overhead while standardizing disposal processes across multiple locations.
These vendors also unlock additional value through remarketing services: retired assets often retain significant market value, allowing companies to recover a portion of their initial investment and offset their Total Cost of Ownership (TCO). This approach generates revenue while advancing sustainability goals by extending equipment lifespans and reducing electronic waste.
Environmental Impact
The environmental impact of our digital lives is significant. Several reports show that the IT industry is responsible for 3% of global CO2 emissions — more than France, Italy, Portugal, and Spain combined.
E-waste is a growing crisis. According to the UN Environment Programme, the world generates 62 million tonnes of e-waste every year — enough to fill 1.5 million transport trucks — with that figure expected to reach 82 million metric tons by 2030. Proper and ethical ITAD practices divert electronic waste from landfills through refurbishing, reselling, or responsible recycling.
Following proper IT asset disposition practices ensures compliance with key regulations like HIPAA, GDPR, and the Sustainable Electronics Recycling Act (SERA), which mandate specific protocols for data protection and e-waste disposal. Companies that fail to comply face severe penalties. According to the HHS’s updated civil monetary penalty amounts for 2025, HIPAA violation penalties now range from $145 per violation to $2,190,294 per violation, depending on the level of culpability. Beyond avoiding these financial risks, organizations that demonstrate commitment to responsible e-waste management strengthen their ESG credentials, which increasingly influence customer choices and investor decisions.
What Should You Look for in an ITAD Provider?
Certifications, verified data security protocols, and a commitment to reuse over recycling. Not all ITAD providers are created equal — here’s how to separate the serious players from the risky ones.
Industry Certifications
Certifications are your first line of defense against subpar service. Several key certifications serve as critical benchmarks for ensuring compliance with environmental, data security, and social responsibility standards:
-
R2 (Responsible Recycling): Focuses on environmentally responsible recycling practices and data security. ITAD vendors must adhere to strict guidelines that ensure minimal environmental impact and secure data destruction. R2 certification is administered by Sustainable Electronics Recycling International (SERI) and requires regular audits to maintain compliance.
-
e-Stewards: Developed by the Basel Action Network (BAN), this certification builds upon R2 standards by adding requirements related to human rights and worker safety. e-Stewards certified vendors must ensure that electronic waste is not exported to countries where it may be processed in unsafe conditions — emphasizing comprehensive environmental responsibility and advanced data security practices.
-
NAID AAA: The National Association for Information Destruction offers this certification specifically for data destruction services. It mandates rigorous procedures for securely destroying data from electronic devices, including employee screening and strict chain-of-custody protocols. NAID AAA certification helps businesses ensure that their sensitive information is handled securely throughout the disposal process.
-
ISO 14001: This international standard focuses on effective environmental management systems. While not exclusive to ITAD, it’s highly relevant — compliance with ISO 14001 demonstrates a commitment to sustainability in IT asset disposal.
Don’t stop there. Look for providers with Appendix B (logical data sanitization) and Appendix C (test and repair) certifications as well. These extras show a commitment to thorough data destruction and equipment refurbishment. Make sure they are HIPAA compliant too.
Prioritize providers that emphasize reuse over recycling. Look for companies that test and repair devices, giving them a second life whenever possible. It’s not just good for the planet — it can be good for your bottom line. Ask for transparent reports on environmental impact. A truly responsible ITAD provider will be proud to show off their green credentials.
Data Security Protocols
"Trust me" isn’t good enough when your organization’s data is at stake. IT departments must thoroughly evaluate providers’ security protocols through specific documentation, certifications, and processes.
A robust chain of custody — like the one Human-I-T offers — forms the foundation of secure IT asset disposition. This documented timeline tracks each asset from the moment it leaves your facility until its final disposition, recording every transfer, storage location, and processing step. This documentation proves crucial for both security audits and regulatory compliance, particularly in industries governed by HIPAA or GDPR. Without it, organizations cannot verify that their assets — and the sensitive data they contain — remained secure throughout the disposition process.
When evaluating an ITAD provider’s security protocols, require documentation of:
- NAID AAA certification for data destruction services
- Detailed data sanitization methods that align with NIST 800-88 guidelines
- Employee background check procedures and security clearances
- Facility security measures, including surveillance systems and access controls
- Regular third-party security audits
- Real-time asset tracking capabilities
- Destruction certificates for each processed device
Ask potential providers for their incident response plan and data breach notification procedures. A reputable ITAD partner should provide sample documentation of their security reports, destruction certificates, and chain of custody records during the evaluation process. These documents should detail specific methods used, timestamps, responsible personnel, and verification steps.
The provider should also maintain detailed records of their security certifications, employee training programs, and facility security measures. Regular security audits by independent third parties offer additional verification. Request evidence of these audits and their results as part of your due diligence process.
Comprehensive Service and Transparency
The best ITAD providers offer a one-stop shop for all your digital disposal needs. From data center decommissioning to e-waste recycling, look for a partner that can handle it all. This comprehensive approach ensures consistency and simplifies the process for your organization.
But services are only half the equation. Your ITAD provider should be able to track every asset from the moment it leaves your premises to its final disposition. We also recommend that your chosen provider be willing to undergo third-party audits. This openness to external verification demonstrates a commitment to compliance and best practices.
Choosing the right ITAD provider is a crucial decision that impacts your data security, environmental footprint, and regulatory compliance. By focusing on these key considerations, you’ll be well-equipped to find a partner that aligns with your business needs and values.
What Are the Best ITAD Practices for Organizations?
Start with a comprehensive policy, invest in the right tools, and build security awareness into your organizational culture. Here’s how.
Strategy and Tools
First things first: you need a game plan. A detailed ITAD policy is your roadmap, covering everything from asset repair to media cleansing and disposal guidelines.
Don’t go it alone. Assemble a cross-functional team for policy development — bring together voices from IT, finance, legal, and sustainability. You’ll create a policy that addresses all angles of ITAD.
You can’t manage what you can’t measure. An IT Asset Management (ITAM) system is essential. Think of it as a digital inventory for your tech. ITAMs effectively track and manage IT assets throughout their lifecycle with features like lifecycle management, automated asset discovery, software license management, and reporting and analytics. Regular asset tracking ensures you know exactly what you have, where it is, and when it’s time for an upgrade or retirement.
Build a Culture of IT Security
Your employees are on the front lines of data security. Make sure they’re armed with knowledge. Implement ongoing training programs to educate employees about the importance of ITAD, data security protocols, and environmental sustainability practices. Regular sessions reinforce the significance of these practices and keep employees updated on policy or regulation changes.
Foster a culture of responsibility by involving employees in the ITAD process. Encourage them to participate actively in asset tracking and disposal efforts. Create feedback channels where employees can ask questions and express concerns.
Most importantly, educate employees about relevant data protection regulations — GDPR, HIPAA — and the consequences of non-compliance. Understanding these legal frameworks motivates strict adherence to ITAD policies. After all, even the best ITAD strategy can be undermined by a single careless action.
Integrate ITAD into Broader Sustainability Initiatives
SERI’s "The Journey from ITAD to Sustainable ITAD" report encourages us to think bigger. Don’t treat ITAD as an isolated process. Integrate it into your broader IT and sustainability initiatives. This might mean rethinking your upgrade cycles or opting for repair over replacement when possible. It’s not about disposing of old tech — it’s about creating a more sustainable IT ecosystem.
SERI also emphasizes the importance of maximizing reuse in your ITAD process. This starts with thoughtful collections — ensuring devices are handled carefully to preserve their potential for a second life. A step as simple as removing administrative locks before disposal can make a big difference.
By implementing these best practices, you’re creating a comprehensive ITAD strategy that protects your data, your bottom line, and the environment.
FAQ
What is ITAD and why does it matter?
ITAD stands for IT Asset Disposition — the process of securely retiring end-of-life technology through data destruction, refurbishment, and responsible recycling. It matters because improperly disposed technology exposes organizations to data breaches (averaging $4.44 million per incident, according to IBM’s 2025 report), regulatory fines, and environmental liability.
How does ITAD protect my organization from data breaches?
Certified ITAD providers use data sanitization methods that adhere to NIST 800-88 guidelines, including multi-pass data wiping, degaussing, and physical destruction. Each step is externally verified and documented with destruction certificates, creating an auditable chain of custody from your facility to final disposition.
What certifications should an ITAD provider have?
Look for R2 (Responsible Recycling), e-Stewards, NAID AAA for data destruction, and ISO 14001 for environmental management. Additional Appendix B and Appendix C certifications indicate a provider’s commitment to thorough data sanitization and device refurbishment. HIPAA compliance is essential for healthcare organizations.
Can retired IT assets generate revenue for my organization?
Yes. A strategic ITAD program can transform technology disposal from a cost center into a value-generating operation. Retired assets often retain significant market value. ITAD providers with remarketing services can recover a portion of your initial investment, offsetting your Total Cost of Ownership while advancing sustainability goals through reuse.
How can Human-I-T help with my organization’s ITAD needs?
Human-I-T provides comprehensive ITAD services that include secure data destruction with a documented chain of custody, device refurbishment, and responsible recycling. As a nonprofit focused on digital equity, Human-I-T gives refurbished devices a second life by distributing them to underserved communities — meaning your retired technology directly closes the digital divide. Contact Human-I-T today to discuss your specific ITAD requirements.
Get Your ITAD Questions Answered Today
Human-I-T’s team of ITAD professionals specializes in helping organizations navigate the complexities of technology retirement while ensuring maximum security and compliance.
Contact us today to learn how our secure ITAD services can protect your sensitive data, keep e-waste out of landfills, and give retired technology a second life in the hands of families who need it most.