Editor’s Note: This article was originally published in 2023 and updated in November 2025 to reflect current data breach costs, e-waste statistics, emerging threats like AI and IoT device sanitization, and the latest NIST 800-88 Rev. 2 standards.
Table of Contents
- TL;DR
- Why Isn’t Deleting Files Enough to Protect My Data?
- What Threats Make Data Sanitization Urgent Right Now?
- What Is the Difference Between Data Sanitization and Data Destruction?
- What Are the Top 5 Data Sanitization Tools?
- Why Are AI, IoT, and Cloud Devices So Much Harder to Sanitize?
- What Other Challenges Do IT Teams Face With Data Sanitization?
- How Does Human-I-T Handle Data Sanitization Securely?
- FAQ
TL;DR
Data sanitization—rendering data permanently irretrievable while preserving a device for reuse—is fundamentally different from simply deleting files or destroying hardware. According to IBM’s 2025 Cost of a Data Breach Report, the average data breach costs $4.44 million globally, and improperly disposed devices are an overlooked attack vector. The top five sanitization tools include advanced overwriting software, degaussing, specialized SSD erasure, physical destruction, and encryption-based wiping—each suited to different device types and security requirements. Choose a NAID AAA-certified partner like Human-I-T to ensure compliance and give devices a second life.
Introduction
Your company’s old laptop sits in storage. A tablet collects dust in a drawer. A server awaits decommissioning. Each device holds a universe of data—customer records, financial information, strategic plans, trade secrets.
What happens when these devices reach the end of their useful life? That’s where many companies make costly mistakes. According to IBM’s 2025 Cost of a Data Breach Report, the average data breach now costs businesses $4.44 million globally—a 9% decrease from last year and the first decline in five years—yet a staggering $10.22 million in the United States, where regulatory penalties and detection costs continue to climb. Even more alarming: 97% of AI-related breaches involved systems without proper access controls. Devices you thought were "deleted" can become your biggest security vulnerability.
Data sanitization isn’t optional housekeeping. It’s your commitment to protecting what matters most: your customers’ trust, your company’s reputation, and your legal standing.
Why Isn’t Deleting Files Enough to Protect My Data?
Because deletion doesn’t actually erase anything. It simply marks storage space as available while leaving the original data fully intact underneath.
According to NIST Special Publication 800-88, traditional deletion leaves residual data traces that specialized recovery tools can easily retrieve. Your "deleted" files remain on the drive, invisible to you but accessible to anyone with the right software.
This isn’t a hypothetical. Secureframe reports that malicious insider attacks now cost an average of $4.92 million per breach—the highest among all threat vectors. That old laptop you donated without proper sanitization? It could be the entry point for your next data breach.
What Threats Make Data Sanitization Urgent Right Now?
The cybersecurity landscape in 2025 and 2026 is more dangerous than ever—and improperly sanitized devices sit at the intersection of every major threat vector.
Ransomware Is Devastatingly Costly—and Accelerating
According to IBM’s 2025 report, the average cost of a ransomware or extortion incident reached $5.08 million when attackers disclosed the breach. Global ransomware attacks rose 32% in 2025, with 7,419 attacks recorded worldwide compared to 5,631 in 2024. Yet only 40% of organizations now involve law enforcement, down from 52% the previous year. Companies are facing these threats increasingly alone.
Bright Defense notes that 63% of ransomware victims now refuse to pay, up from 59% the previous year. Companies are getting smarter about not paying—but the financial toll from recovery, downtime, and reputational damage remains enormous.
AI-Driven Attacks Are Multiplying
One in six breaches in 2025 involved AI-driven attacks, according to IBM. Among those AI-enabled breaches, 37% used phishing attacks and 35% used deepfake attacks. Meanwhile, Microsoft’s Cyber Signals 2025 recorded a 46% rise in AI-generated phishing content.
Security Magazine reports that AI tools like ChatGPT and Microsoft Copilot contributed to millions of data loss incidents in 2024. When employees paste sensitive data into AI tools, that information often leaves your company’s control forever.
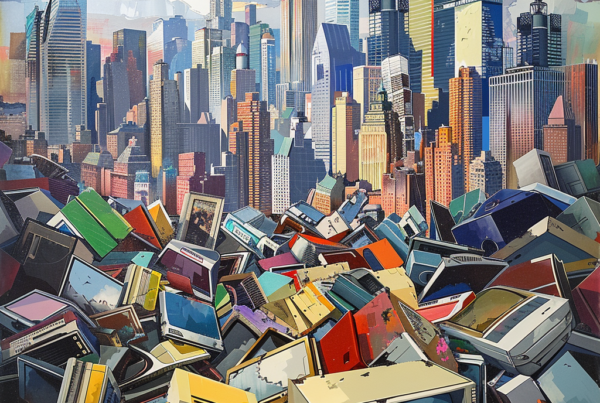
The E-Waste Crisis Compounds the Problem
The digital revolution creates physical waste—and physical waste creates security risk. According to the UN’s Global E-Waste Monitor 2024, the world generated a record 62 million metric tons of e-waste in 2022, an 82% increase from 2010. By 2030, that number is projected to reach 82 million metric tons.
Here’s the connection corporate leaders miss: only 22.3% of e-waste was properly collected and recycled in 2022. The rest? Dumped, burned, or processed through informal channels where data recovery is trivial.
Your improperly sanitized devices become tomorrow’s data breaches.
What Is the Difference Between Data Sanitization and Data Destruction?
They are not interchangeable—and the distinction determines whether your retired devices become e-waste or get a second life.
Data destruction means making a device completely unusable. Smashing a hard drive with a hammer? That’s destruction. It works, but it creates e-waste and eliminates any possibility of device reuse.
Data sanitization renders data irretrievable while preserving the device for reuse or responsible recycling. It’s more sophisticated, more environmentally responsible, and—when done correctly—equally secure.
NIST defines media sanitization as "a process that renders access to target data on the media infeasible for a given level of effort." The goal isn’t just deletion. It’s making data recovery impossible, even in a laboratory setting.
For organizations that care about both security and environmental impact, sanitization is the clear choice. You protect your data and keep functioning devices out of landfills—where they can be refurbished and distributed to families who need them.
What Are the Top 5 Data Sanitization Tools?
The right tool depends on your device type, security requirements, and whether you want the hardware to live on. Here are the five categories every IT team should know.
1. Advanced Overwriting Software (e.g., DBAN)
Best for: Magnetic drives where data needs to be wiped without destroying the device.
Thorough overwriting ensures data is irretrievable, aligning with standards like ISO 27040. The trade-off: it’s time-consuming, and it may not be fully effective for SSDs due to their unique architecture. For traditional hard drives headed toward refurbishment, overwriting remains a reliable workhorse.
2. Degaussing (e.g., Garner HD-3WXL)
Best for: Bulk erasure of magnetic media where device reuse isn’t a priority.
Degaussing uses powerful magnetic fields to render data unreadable—quickly and efficiently. The limitation is significant: devices become unusable afterward, and the method is completely ineffective for SSDs. Think of degaussing as the nuclear option for magnetic media.
3. Specialized SSD Erasure (e.g., Blancco Drive Eraser)
Best for: SSDs that need thorough data wiping while preserving the device for reuse.
SSDs use wear-leveling algorithms that scatter data across memory cells, making traditional overwriting unreliable. Specialized SSD erasure tools address these architecture-specific challenges. They require dedicated software and sometimes additional licenses, but they’re essential for any organization decommissioning modern devices.
4. Physical Destruction (e.g., SEM Model 0101)
Best for: Situations where absolute security assurance is required and device reuse isn’t a concern.
Shredding, crushing, or incinerating a drive gives you complete certainty that data can never be retrieved. The downside: you’ve just created e-waste. For devices containing the most sensitive data—classified government information, certain healthcare records—physical destruction may be warranted. For everything else, consider sanitization methods that preserve the hardware.
5. Encryption-Based Wiping (e.g., VeraCrypt)
Best for: Versatile data protection across various storage types.
Encryption-based wiping adds an extra security layer before deletion—encrypt the entire drive, then destroy the encryption key. The data remains on disk but is rendered permanently unreadable. This approach works across diverse storage mediums, though the encryption process can be resource-intensive and isn’t ideal for rapid, high-volume sanitization.
Why Are AI, IoT, and Cloud Devices So Much Harder to Sanitize?
Traditional sanitization methods were designed for traditional devices. Today’s technology—AI systems, IoT hardware, and cloud-connected devices—presents challenges that standard tools weren’t built to handle.
AI Systems and Training Data
When your company uses AI tools, where does your data actually go? CISA’s May 2025 guidance warns that AI data security risks include data poisoning, statistical bias, and adversarial machine learning threats. Once sensitive data enters an AI model’s training set, standard sanitization won’t remove it.
The Hacker News reports that AI has become the number one data exfiltration channel in enterprises. Employees routinely paste sensitive information into ChatGPT or Copilot, often without realizing the data has left company control.
Before decommissioning devices used with AI tools, you must identify which devices accessed AI platforms, clear browser histories and cached credentials, remove locally stored AI interaction logs, and determine whether cloud-stored AI interactions need separate deletion.
IoT Devices Create Dangerous Blind Spots
Your company’s network likely contains dozens of connected devices you’ve never inventoried. Smart thermostats. Security cameras. Badge readers. Printers with hard drives.
Device Authority research shows IoT devices often lack encryption for regular transmissions and ship with insecure default settings. Many lack user-accessible interfaces for data deletion. Proprietary operating systems require manufacturer-specific tools. Limited computational power makes traditional overwriting slow. And some devices store data in cloud accounts that must be separately addressed.
Disposing of these devices without proper sanitization creates security vulnerabilities that most organizations never even see.
Cloud-Connected Devices Need Special Handling
Your laptop connects to Google Drive. Your tablet syncs with iCloud. Your phone backs up to multiple cloud services. Sanitizing the physical device doesn’t sanitize cloud-stored data.
Votiro’s 2025 analysis emphasizes that organizations must identify all structured and unstructured data sources feeding into cloud platforms before decommissioning any device. Miss one sync point and you’ve left a data trail that no amount of on-device wiping will eliminate.
What Other Challenges Do IT Teams Face With Data Sanitization?
Even seasoned IT professionals stumble on these five problems. Knowing them in advance is half the battle.
Data Remanence in Advanced Storage
Modern NAND-based SSDs use wear-leveling algorithms that create multiple copies of data blocks, making traditional overwriting less effective. The fix: use sanitization methods specifically designed for SSDs—cryptographic erasure or the device’s built-in secure erase command. Stay current with the latest sanitization standards as storage technology evolves.
Remote Work and BYOD Policies
Ensuring consistent data sanitization across diverse devices and operating systems is a significant challenge when employees use personal hardware for work. A centralized device management system can push mandatory sanitization protocols and software updates to all registered devices, ensuring uniformity in data protection regardless of who owns the hardware.
Overlooked Auxiliary and Cached Data
Beyond primary storage, devices contain auxiliary data in slack space, RAM, and temporary files. Cached data—often overlooked—is a goldmine for cybercriminals. Comprehensive sanitization tools that scan and sanitize the entire device, including all potential data pockets, are essential. Regular audits help identify blind spots before attackers do.
Balancing Speed With Thoroughness
Quick sanitization processes might not be thorough. Comprehensive methods are time-consuming, especially for larger enterprises with vast device inventories. A tiered approach works: critical data undergoes rigorous sanitization processes while less sensitive data uses quicker methods. This optimizes both time and security.
Regulatory and Compliance Hurdles
Different industries and regions have varying data protection regulations. Healthcare, finance, government, education—each carries its own compliance requirements. Automated compliance tools and regular training sessions help IT teams navigate this complex landscape without sacrificing operational efficiency.
How Does Human-I-T Handle Data Sanitization Securely?
Most companies face a difficult choice: destroy devices to ensure security, or reuse them and risk data exposure. Human-I-T eliminates that trade-off.
Our data sanitization process meets the highest industry standards. We hold NAID AAA Certification—the gold standard for information destruction. That means NIST 800-88 compliant sanitization using DoD and HIPAA-approved methods, 100% verification that data has been irretrievably erased, serialized reporting showing exactly what happened to each device, certificates of destruction for your compliance records, and R2 and ISO certification for any devices requiring physical destruction.
For organizations handling particularly sensitive data, we offer on-site data destruction at your location in Los Angeles and surrounding areas. Your devices never leave your facility until they’re completely sanitized.
Secure Chain of Custody
Worried about what happens to your devices in transit? Our secure pickup service uses GPS-tracked trucks equipped with four cameras providing continuous monitoring. You can watch your devices being loaded and track them in real-time to our NAID-certified facility. Every device is logged with serial numbers, physically secured in ISO-certified facilities, protected by advanced ADT security systems, and handled only by background-checked personnel.
Your Devices Get a Second Life
Here’s what makes Human-I-T fundamentally different from a standard ITAD provider. After your data is securely and verifiably destroyed, our technicians refurbish viable devices and distribute them to income-qualified families who lack access to technology. Your retired hardware doesn’t become e-waste. It becomes a bridge across the digital divide.
It’s about valuable resources being repurposed. It’s about toxic materials staying out of landfills. And it’s about working families gaining the tools they need to thrive in a digital world.
Contact us today to learn how our secure ITAD services can protect your business data while closing the digital divide. Because the best time to start proper data sanitization was yesterday. The second-best time is now.
FAQ
What is data sanitization and how is it different from deleting files?
Data sanitization is a process that renders data permanently irretrievable from a storage device—even with forensic recovery tools. Deleting files or formatting a drive simply marks space as available while leaving the original data intact underneath. According to NIST 800-88, proper sanitization makes data recovery "infeasible for a given level of effort," which standard deletion does not achieve.
Which data sanitization method is best for SSDs?
Traditional overwriting methods are unreliable for SSDs because of their wear-leveling architecture. Specialized SSD erasure tools like Blancco Drive Eraser, cryptographic erasure, or the device’s built-in secure erase command are designed to address these challenges. For maximum assurance, use a tool that provides a verified certificate of sanitization.
Do I need to sanitize IoT devices before disposal?
Yes. IoT devices—smart thermostats, security cameras, badge readers, and even network printers—often store sensitive data and credentials. Many lack user-accessible interfaces for deletion, so disposal without sanitization creates blind spots that attackers can exploit. Work with a certified ITAD provider that has the tools and expertise to handle proprietary IoT systems.
How can I ensure my company meets data sanitization compliance requirements?
Partner with a NAID AAA-certified provider that follows NIST 800-88 guidelines and can furnish serialized reports and certificates of destruction. Human-I-T’s ITAD services include DoD and HIPAA-approved sanitization methods, R2 and ISO certification, and full chain-of-custody documentation—covering compliance requirements across healthcare, finance, government, and education.
Can sanitized devices be reused instead of destroyed?
Absolutely—and they should be. Proper data sanitization preserves hardware for reuse, keeping functional technology out of landfills. Human-I-T refurbishes sanitized devices and distributes them to income-qualified families, turning your company’s retired hardware into digital equity. Donate your technology and protect your data while making a measurable impact.